Blogs & News
How to deal with compromised business mailboxes & secure your business sensitive data
8 December 2021
Summary – Protecting business sensitive data
By compromising your business emails, hackers can access any business sensitive data within your mailbox and can add forwarding rules without your knowledge, this can lead to a GDPR data breach, as personal data can be lost.
An email account can be compromised in a number of different ways. In some cases, your password may be weak and easily guessed or obtained through a public breach. In other cases, you may have clicked on a malicious link in an email, social networking site, or webpage. Or, you may have downloaded an app or file that contained malicious scripts.
The most common way business mailboxes get hacked are through phishing schemes. Phishing is usually done by sending out an email that looks legitimate and sends the recipient to a fake website and has them enter credentials to “verify” information, which is then stolen.
How can I deal with a compromised mailbox?
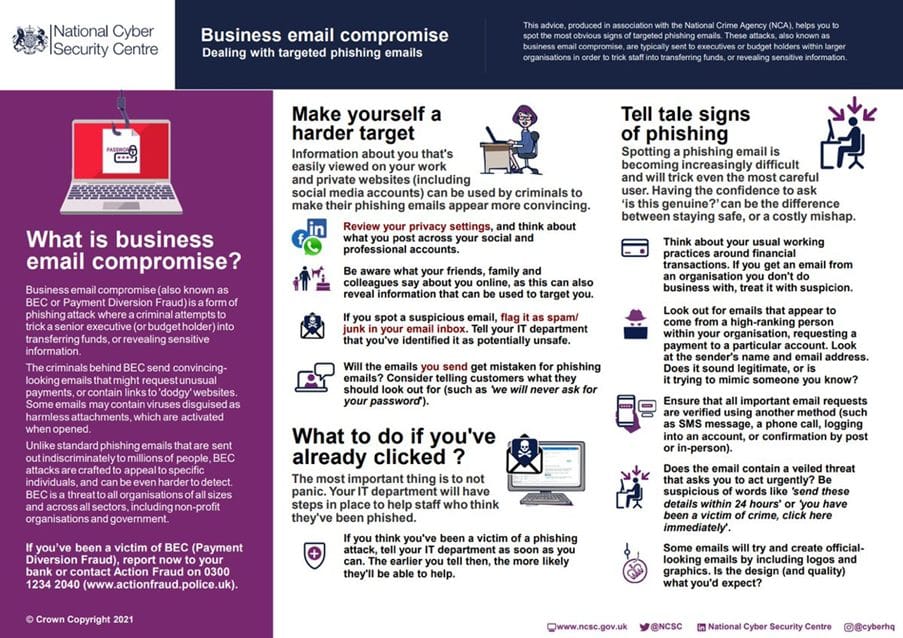
Below is a diagram from the National Cyber Security Centre (GCHQ) which outlines how to make yourself a harder target, some tell tale signs of phishing and what to do if you’ve already clicked.
Further Information
If you have any questions about this or need assistance, then please contact the GCC Group Support Team on 0345 260 1151 or servicedesk@gccgroup.co.uk
The importance of IT security
At work and in our daily lives we have become increasingly reliant on technology. IT security is paramount for the modern business.
When systems are impacted by digital threats, it can be difficult and time-consuming to recover operations efficiently.
You need a plan to ensure whatever the threat to your business, your systems remain secure and operational with limited disruptions.
Our skilled experts will work with you to ensure your team makes all the necessary preparations to stay safe and be more resilient in the event of technical problems.
GCC Security services:
